A new variant of the wiper malware AcidRain, known as AcidPour, has been discovered by SentinelOne’s threat intelligence team, SentinelLabs.
AcidRain is destructive wiper malware attributed to Russian military intelligence.
In May 2022, AcidRain was used in a broad-scale cyber-attack against Viasat’s KA-SAT satellites in Ukraine.
The malware rendered KA-SAT modems inoperative in Ukraine and caused additional disruptions throughout Europe at the onset of the Russian invasion.
AcidPour Shows Proximity with AcidRain
On March 16, 2024, SentinelLabs researchers Juan Andrés Guerrero-Saade and Tom Hegel began observing a suspicious Linux binary uploaded from Ukraine.
They quickly realized that this activity showed surface similarities with malicious activities originating from AcidRain.
The new malware they observed also showed behaviors similar to AcidRain’s, such as targeting specific directories and device paths common in embedded Linux distributions.
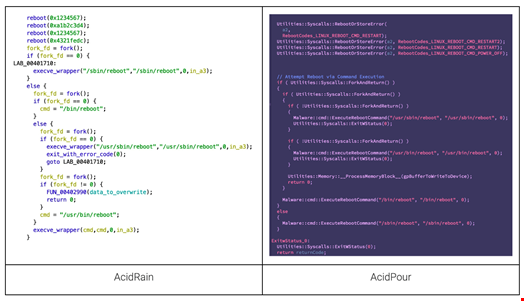
However, the new malware seemed to expand upon AcidRain’s capabilities and destructive potential to include Linux Unsorted Block Image (UBI) and Device Mapper (DM) logic.
UBI is a volume management system specifically designed for raw flash memory devices, such as those found in solid-state drives (SSDs) and embedded systems.
DM is a Linux system that acts as a translator between applications (e.g., filesystems) and physical storage devices.
They called the new variant AcidPour.
It’s been an interesting weekend! Eagle-eyed @TomHegel spotted what appears to be a new variant of AcidRain. Notably this sample was compiled for Linux x86 devices, we are calling it ‘AcidPour’. Those of you that analyzed AcidRain will recognize some of the strings. Analysis 🧵 pic.twitter.com/wY3PJKaOwK
— J. A. Guerrero-Saade (@juanandres_gs) March 18, 2024
“Our technical analysis suggests that AcidPour’s expanded capabilities would enable it to better disable embedded devices including networking, Internet-of-Things (IoT), large storage (RAIDs), and possibly industrial control systems (ICS) devices running Linux x86 distributions,” wrote SentinelLabs researchers.
AcidPour Attributed to Sandworm Subcluster
Although the SentinelLabs analysis showed proximity between AcidRain and AcidPour, the researchers assessed that the two programs’ codebases only overlap by an estimated 30%.
This suggests that AcidPour could have been developed by a different threat actor.
Following Saade and Hegel’s initial reporting on X it was reported that the Ukrainian SSCIP attributed AcidPour to UAC-0165, a subgroup of what is known as Sandworm.
Sandworm is an advanced persistent threat (APT) group believed to be operated by Unit 74455, a cyberwarfare unit of Russia’s military intelligence service (GRU).
The SentinelLabs findings coincide with the enduring disruption of multiple Ukrainian telecommunication networks, reportedly offline since March 13. The malicious campaign was publicly claimed by a GRU-operated hacktivist persona via Telegram.
The NSA Director Rob Joyce said on X that it is “a threat to watch.”
“My concern is elevated because this variant is a more powerful AcidRain variant, covering more hardware and operating system types,” he added.
This is a threat to watch. My concern is elevated because this variant is a more powerful AcidRain variant, covering more hardware and operating system types. https://t.co/h0s6pJGuzv
— Rob Joyce (@NSA_CSDirector) March 19, 2024
In their report, SentinelLabs’ Guerrero-Saade and Hegel concluded: “The transition from AcidRain to AcidPour, with its expanded capabilities, underscores the strategic intent to inflict significant operational impact. This progression reveals not only a refinement in the technical capabilities of these threat actors but also their calculated approach to select targets that maximize follow-on effects, disrupting critical infrastructure and communications.”
Credit: Source link

Comments are closed.