Identity & Access Management
,
Security Operations
Plug and Play Ventures Left an Amazon S3 Bucket Open to the Internet

A Silicon Valley venture capital firm that runs a matchmaking service linking investors with startups exposed 6GB of data, including deal flow information pertaining to investors and startups.
See Also: Marching Orders: Understanding and Meeting the Biden Administration’s New Cybersecurity Standards
The data belongs to Plug and Play Ventures, which is headquartered in Sunnyvale, California, and has offices around the world. Plug and Play helps startups get off the ground and match those companies with investors. The firm itself says it has benefited from early investments in PayPal and Dropbox.
The leaked data appears to be a PostgreSQL database for Playbook.vc, a networking and deal flow application from Plug and Play.
The unencrypted data includes personal contact information for investors, founders and CEOs. It includes personal information voluntarily submitted by those people to Plug and Play, including names, phone numbers and email addresses. There are more than 50,000 unique email addresses in the data.
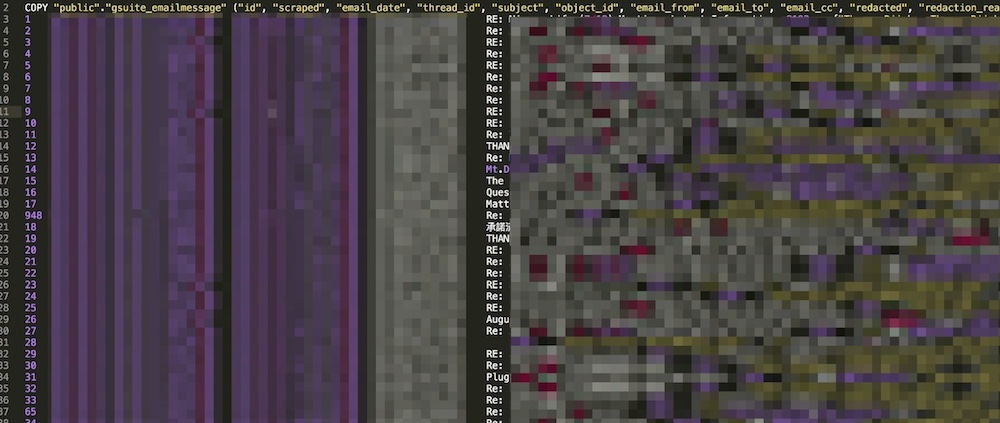
In other parts of the data there are snippets of emails – such as the sender, recipient and subject line of an email – that were sent between staff at Plug and Play and other users. The content of those emails, however, doesn’t appear to be in the data. The data appears to have been scraped from G Suite, which is now known as Google Workspace.
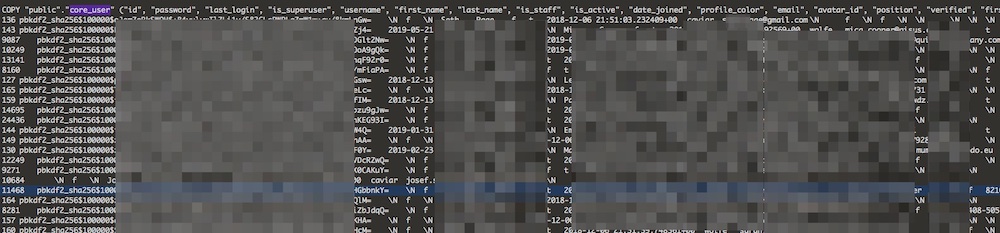
There was also an exposed API key, although it isn’t clear what kind of data that unlocks. Also, usernames and password hashes were exposed. Plain-text passwords are hashed, which is the term for running a password through an algorithm. That cryptographic output is retained rather than the actual password, which is safer in case of a data breach. The hashes appear to be pbkdf2 SHA256.
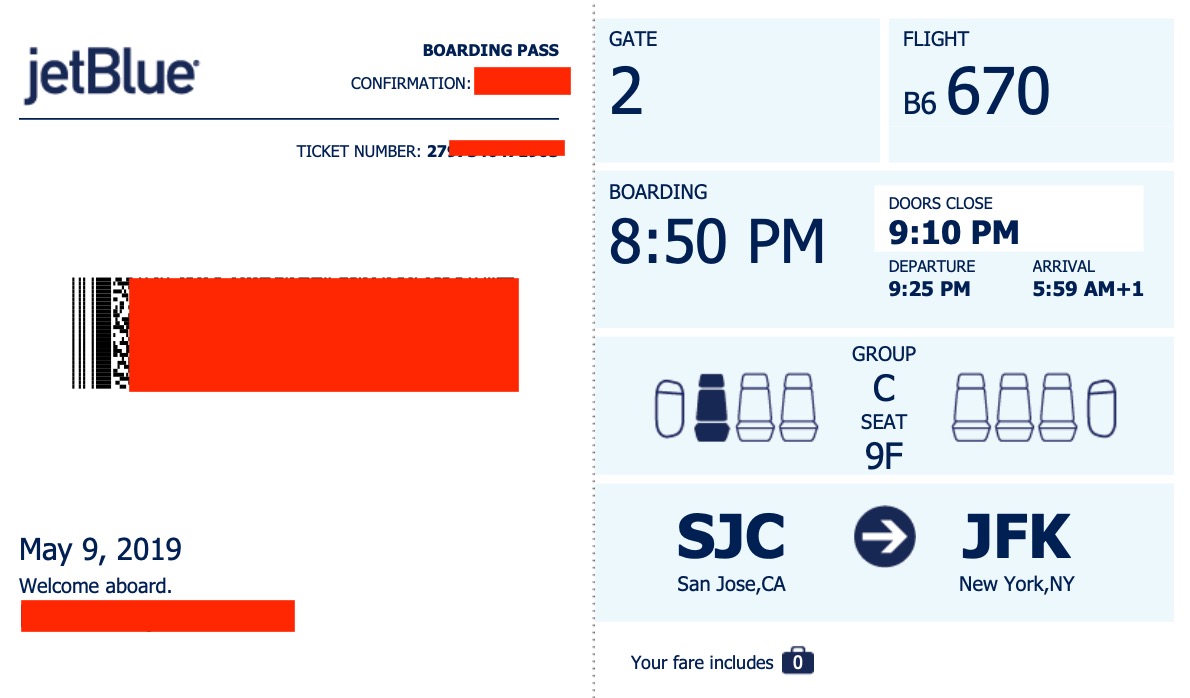
ISMG found other documents, including a boarding pass and dozens of slide decks written by companies for investors, with at least one marked “confidential.” There are also logs of IP addresses and what pages those addresses visited.
The data would appear to give some clues as to what types of companies an investor may be interested in, which could perhaps give an edge in the ultra-competitive sphere of startup investment.
Exposed for a Year
The data appears to have been exposed to the public since Oct. 20, 2020, due to a misconfiguration of an Amazon S3 storage bucket, according to the researcher who found it. The researcher wishes to remain anonymous.
ISMG notified Plug and Play of the breach on Sept. 16. Syed Azhar, who is Plug and Play’s chief information officer, responded on Sept. 17.
Despite the contact, the data exposure continued. Finally, by Oct. 2, the data was secured after a tweet the previous day by Australian security researcher Troy Hunt, who created the Have I Been Pwned data breach notification service.
Anyone got a contact at @PlugandPlayTC that can take a serious security issue seriously? The kind of issue that usually results in a company sending a letter beginning with “We take security seriously…”
— Troy Hunt (@troyhunt) October 1, 2021
It’s unclear why there was a delay in securing the data. Azhar did not respond to a query as to whether Plug and Play will notify those in the breach or regulators.
Plug and Play’s website has a privacy policy indicating that its U.S. operations fall under California law. California’s data breach law requires notification of residents if their unencrypted personal information “was acquired, or reasonably believed to have been acquired, by an unauthorized person,” according to the state’s Attorney General’s Office.
The company also has offices throughout the European Union, which means if there are E.U. residents in the breach, the General Data Protection Regulation would apply. That requires entities to report data breaches within 72 hours.
Credit: Source link

Comments are closed.